In today's digital landscape, SSH remote device connectivity has become a cornerstone for secure communication between devices and networks. Secure Shell (SSH) is no longer just a protocol; it is a lifeline for IT professionals, developers, and system administrators who need to manage servers, devices, and data remotely. Whether you're configuring a Linux server or troubleshooting a network issue, SSH plays a pivotal role in ensuring both security and efficiency.
As remote work and cloud computing continue to grow, understanding how SSH remote device works is crucial for anyone involved in IT operations. This protocol not only provides encrypted communication but also offers authentication mechanisms that safeguard sensitive information from unauthorized access.
This comprehensive guide will delve into everything you need to know about SSH remote device connectivity. From setting up SSH to troubleshooting common issues, we'll cover it all, ensuring you have the tools and knowledge to manage your devices securely and effectively.
Read also:Emily Compagno Husband A Comprehensive Look Into Her Personal Life And Career
Table of Contents
- Introduction to SSH
- How SSH Remote Device Works
- Setting Up SSH
- Securing SSH Connections
- SSH Commands and Tools
- Common SSH Issues and Solutions
- SSH for Remote Device Management
- SSH Security Best Practices
- The Future of SSH
- Conclusion
Introduction to SSH
Secure Shell (SSH) is a cryptographic protocol designed to provide secure communication over unsecured networks. Originally developed as a replacement for less secure protocols like Telnet, SSH has evolved into a powerful tool for remote device management. Its ability to encrypt data transmissions and authenticate users makes it indispensable in modern IT environments.
SSH operates on port 22 by default and uses public-key cryptography for secure authentication. This ensures that only authorized users can access remote devices, protecting sensitive systems from unauthorized access. As the demand for remote work grows, SSH remote device connectivity has become even more critical.
Why Use SSH for Remote Connectivity?
SSH offers several advantages over other remote access methods:
- Encryption: All data transmitted through SSH is encrypted, preventing eavesdropping and data theft.
- Authentication: SSH supports multiple authentication methods, including password-based and public-key authentication, ensuring secure access.
- Portability: SSH is widely supported across various operating systems, making it versatile for cross-platform environments.
How SSH Remote Device Works
Understanding how SSH remote device connectivity works is essential for leveraging its full potential. At its core, SSH establishes a secure channel between a client and a server. This channel ensures that all communication remains encrypted and private.
When a user initiates an SSH connection, the client and server exchange cryptographic keys to authenticate each other. Once authenticated, a secure session is established, allowing the user to execute commands on the remote device or transfer files securely.
Key Components of SSH
Several key components make SSH remote device connectivity possible:
Read also:Randy Travis Mental Health Understanding The Journey And Triumphs
- Client: The device initiating the SSH connection.
- Server: The remote device or system accepting the SSH connection.
- Public and Private Keys: Cryptographic keys used for authentication and encryption.
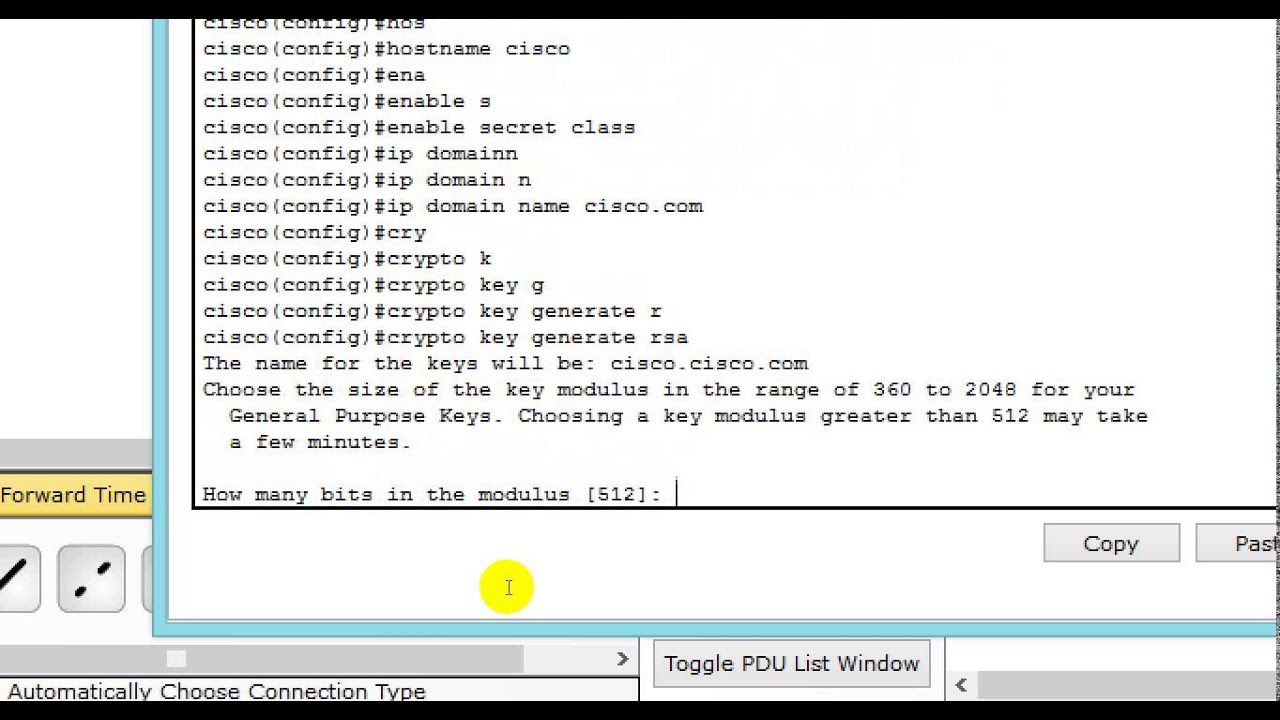
Setting Up SSH
Setting up SSH for remote device connectivity involves configuring both the client and server components. On the server side, you'll need to install and configure an SSH server, while on the client side, you'll need an SSH client to initiate connections.
Most Linux distributions come with OpenSSH pre-installed, making setup relatively straightforward. For Windows users, tools like PuTTY or the Windows Subsystem for Linux (WSL) can be used to establish SSH connections.
Steps to Set Up SSH on Linux
- Install the OpenSSH server package using your distribution's package manager.
- Start the SSH service and enable it to start on boot.
- Configure the SSH server settings in the
/etc/ssh/sshd_configfile. - Restart the SSH service to apply changes.
Securing SSH Connections
While SSH is inherently secure, additional measures can further enhance its security. Implementing best practices for SSH remote device management can protect against potential vulnerabilities and unauthorized access.
One effective method is disabling password authentication and using public-key authentication instead. This eliminates the risk of brute-force attacks targeting weak passwords. Additionally, restricting SSH access to specific IP addresses or subnets can add another layer of security.
Advanced Security Measures
- Disable Root Login: Prevent direct root access to reduce the risk of unauthorized administrative access.
- Change Default Port: Move SSH from its default port (22) to a non-standard port to deter automated attacks.
- Use Firewall Rules: Configure firewalls to allow SSH connections only from trusted networks.
SSH Commands and Tools
SSH offers a wide range of commands and tools to facilitate remote device management. These commands enable users to execute tasks, transfer files, and monitor systems remotely.
Some commonly used SSH commands include:
ssh user@hostname: Establish an SSH connection to a remote device.scp file user@hostname:/path: Securely copy files between local and remote systems.ssh-keygen: Generate public and private keys for authentication.
Popular SSH Tools
Several tools extend the functionality of SSH, making remote device management more efficient:
- PuTTY: A popular SSH client for Windows users.
- WinSCP: A graphical SFTP and SCP client for Windows.
- SSHFS: Allows mounting of remote file systems over SSH.
Common SSH Issues and Solutions
Despite its robustness, SSH remote device connectivity can encounter issues. Understanding common problems and their solutions can help ensure smooth operation.
One frequent issue is connection timeouts, often caused by network instability or misconfigured server settings. Adjusting the ServerAliveInterval and ClientAliveInterval parameters in the SSH configuration file can mitigate this problem.
Troubleshooting Tips
- Check Logs: Review server logs for error messages that may indicate the cause of the issue.
- Test Connectivity: Use tools like
pingandtracerouteto verify network connectivity. - Verify Configuration: Ensure that SSH server settings are correctly configured and not conflicting with other services.
SSH for Remote Device Management
SSH is widely used for managing remote devices, ranging from servers to IoT devices. Its versatility makes it suitable for various applications, from automating tasks to monitoring system performance.
For example, system administrators can use SSH scripts to automate routine maintenance tasks, such as updating software packages or backing up data. Similarly, developers can leverage SSH to deploy applications to remote servers securely.
Use Cases for SSH
- Remote Administration: Manage servers and devices from anywhere with secure access.
- File Transfer: Transfer files securely using SCP or SFTP.
- Automation: Automate repetitive tasks using SSH scripts and tools.
SSH Security Best Practices
Adhering to SSH security best practices is essential for protecting your devices and data. These practices ensure that your SSH remote device connections remain secure and resilient against potential threats.
Regularly updating your SSH server software is one of the most effective ways to maintain security. Updates often include patches for known vulnerabilities, ensuring that your system remains protected.
Best Practices
- Regular Audits: Periodically review SSH logs and configurations to detect and address potential security issues.
- Key Rotation: Rotate SSH keys regularly to minimize the risk of compromised keys.
- Limit Access: Restrict SSH access to only those users who require it for their roles.
The Future of SSH
As technology continues to evolve, so does the role of SSH in securing remote device connectivity. Emerging trends such as quantum computing and advancements in cryptography will shape the future of SSH, ensuring it remains a reliable and secure protocol.
Additionally, the increasing adoption of IoT devices and cloud computing will further highlight the importance of SSH in managing and securing remote systems. Developers and administrators must stay informed about these developments to leverage SSH's full potential.
Emerging Trends
- Post-Quantum Cryptography: Research into quantum-resistant algorithms may influence future SSH implementations.
- Automated Security: AI-driven tools could enhance SSH security by detecting and responding to threats in real-time.
Conclusion
In conclusion, SSH remote device connectivity remains a cornerstone of secure communication in the digital age. By understanding its mechanics, setting it up correctly, and adhering to best practices, you can ensure that your devices and data remain protected.
We encourage readers to share their experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on IT security and remote management. Together, let's build a safer and more connected world!